Free Spotify Social Enegineering
Social engineering is the act of manipulating someone into divulging information or doing something that's not usually in their best interest. In this article, we will look at a few common ways Social Engineers try to manipulate you.
- Spotify Engineering Culture
- Social Engineering Toolkit
- Social Engineering Definition
- Free Spotify Social Engineering Internships
- Spotify Social Media
- Spotify Free Download
Band members wanted. Internships at Spotify are anything but conventional. You won’t be making tea, picking up packages or taking minutes. You’ll be right at the heart of major projects, working with teams of passionate people to create the next awesome thing. After conducting in-depth research, our team of global experts compiled this list of Best Social Engineering Courses, Classes, Tutorials, Training, and Certification programs available online for 2020.This list includes both free and paid courses to help you learn Social Engineering. Delivery Methods – Now that you have your custom-made trojan ready, in this section you will learn a number of social engineering techniques to deliver it to the target, you will learn how to create fake websites that look identical to websites the target trusts, send emails that appear like they’re coming from people the target trusts and use fake login pages and fake updates to hack. We work hard to help you grow your Spotify channel. That’s why you are covered by our 30 days money back guarantee! If you are not completely satisfied and decide to discontinue using our service within 30 days of the first purchase, we’ll promptly refund 100% of your money. Band members wanted. Internships at Spotify are anything but conventional. You won’t be making tea, picking up packages or taking minutes. You’ll be right at the heart of major projects, working with teams of passionate people to create the next awesome thing. After digging through reputable online forums and social media sites, here’s a list of good reads for aspiring social engineers. The books link to their respective product pages on Amazon. Remember, the public library costs nothing. For Howard County locals, search the online catalog before buying books. Deliver Methods – In this section you will learn a number of social engineering methods to deliver trojans to the target, you will learn how to create fake websites that look identical to websites the target trusts, send emails that appear like they’re coming from people the target trusts and use fake login pages and fake updates to hack into the target system, not only that but you.
App spotify premium. We are not affiliated with any website or apps mentioned in the tutorial, and we will recommend respecting the copyright holder’s rights. As far as unlimited skips feature is concerned, it works flawlessly. Hi @jaceandrews:disqus, we have already mentioned in the article above that, “downloading and offline listening option is directly linked to your account so you won’t be able to download any music.”Downloading feature is linked to your account and we cannot enable it with modded apk.
Disclaimer: My articles are purely educational. If you read them and cause damage to someone, that's on you. I don't encourage any malicious activity or black hat practices. Read the code of ethics here.
One common type of scam is the Spanish Prisoner, which dates back to the 18th century and has lots of modern incarnations.
It usually involves someone who's in trouble and needs your help to access their fortune. You just need to wire a few thousand dollars, then they'll pay you back ten times over. But you can guess how that ends.
There are similar scams that have circulated the internet: The IRS scam, Lottery scams, and so on. These are broadly classified as Advance offer scams. You have something waiting for you but you have to pay an advance to receive it.
To the average person, these will seem like poorly executed scam attacks. But these scams have caused thousands of people to lose their hard-earned money. In some cases, their life savings.
These are all examples of social engineering in action.
The idea behind social engineering is to take advantage of a potential victim’s natural tendencies and emotional reactions. Fear and greed are the most vulnerable emotions that are usually taken advantage of by Social Engineers.
Below is a great example of a real-world Social engineering attack.
Types of Social Engineering Attacks
Social engineering can be broadly classified into five types of attacks based on the type of approach used to manipulate a target. Let's go through each one of them.
Spamming (Email, Text, Whatsapp)
Spamming involves sending messages to large groups of people whose contact info is usually obtained through nefarious methods. Spamming is a general term used to define both malicious and non-malicious message broadcasting.
Non-malicious spamming is used by advertisers who try to promote their products to random strangers by emailing them in bulk. Their motive is not to cause damage, but to try and get people to buy their products or promote their services.
Malicious spamming includes messages that try to lure users to the attacker’s website to divulge personal information. This information is then used to craft targeted phishing/vishing attacks on the potential victim.
Phishing (and Vishing)
When the attacker uses text messaging, email, or voice calling (voice phishing = vishing), it is called Phishing.
Phishing is used to make the target believe they are being called by a legitimate institution or an entity in order to extract valuable information from the target.
If someone calls your company pretending to be your printer supplier, they might be able to gain specific information about the printer — the model, IP address (if connected to the internet), and so on.
And once this information is given, the printer might be attacked in order to gain access to your internal network.
Email-based phishing attacks are also common. An attacker can email someone in your company pretending to be Facebook. Once a team member clicks a link, they will end up on a page that looks like Facebook, asking them for their login information. This login information will be sent to the attacker’s server after which they have complete access to the victim’s Facebook account.
The major difference between Phishing and Scamming is that phishing attacks are highly targeted. The attacker knows whom they want to attack and what type of information they are looking for.
Baiting
Baiting involves designing a trap and waiting for the potential victim to walk into the trap. As a simple example, if an attacker drops a few USB drives in your company’s parking lot, chances are, one of your employees will try and plug it into their computer to check the contents of the USB drive.
This might sound silly but there have been numerous instances where simple tricks by Social Engineers have resulted in massive corporate data breaches. It is usually easy to bait people with scams such as the Advance offer scams that are still circulating the internet, feeding on gullible people.
Another common type of baiting is found in pirated software. The attacker will embed malicious software within a popular operating system or a movie for the victim to download. Once the victim downloads and runs the software, the malicious code executes on the victim’s system, and the attacker gains full access to the victim’s machine.
PiggyBacking
PiggyBacking means using someone else to attack a potential victim. The attacker will use a third-party (usually innocent) who has access to the victim in order to carry out a piggybacking attack.
There are many variations of Piggybacking. If an attacker follows your employee to your office using their access card, this is one form of piggybacking called tailgating.
There have been many cases of piggybacking attacks, especially for classified information. Vendor companies that supply hardware/software to government organizations are usually the target of piggybacking attacks.
Once these vendors are compromised, it is easy to attack the target institution since the vendor already has a level of access to the target.
Piggybacking is also associated with some forms of active Wiretapping. The attacker will use a legitimate connection of the victim in order to eavesdrop on the network.
/missing-out-if-do-not-download-new-spotify.html. Choose File→Exit in Windows (XP, Vista, or 7) or choose Spotify→Quit Spotify on the Mac. Make sure you’re installing the latest version of Spotify directly from Spotify’s download page. Ensure that you’ve downloaded the very latest software update for your operating system, which can often smooth out. Find out how to set up and use Spotify. Learn about features, troubleshoot issues, and get answers to questions. Everything you need to stay in tune. Once you do that, go to Apps in Settings, tap Spotify, tap Storage, tap a new option 'Change' under 'Storage used' and select external SD. Wait for a bit until the Spotify app gets moved to the SD. Go back to the home screen, open Spotify, verify SD setting for storage and re-enable your downloads. Check out Spotify Answers for solutions to a wide range of topics. Recently upgraded to iPhone X and new operating system, and now I’m having same issue. I like spotify, but the download button missing seems like an easy fix. If you won't pay attention to small details like this, you'll lose more customers besides me.
Water Holing
Water Holing takes into account the routine actions of the target and using one of those actions to gain unauthorized access. For example, an attacker will find the websites that the target uses on a daily basis and tries to install malware on one of those websites.
The name “Water Holing” is derived from the fact that predators in the wild often wait for their prey near their common watering holes.
An example is the 2019 Holy Water Campaign, which targeted Asian religious and charity groups. The website was compromised after which the visitors were asked to install Adobe Flash on their browsers.
Since Adobe Flash has a number of vulnerabilities, it was easy for the attackers to then execute malicious code on the victim’s machines. Watering hole attacks are uncommon but they pose a considerable threat since they are very difficult to detect.
Protecting Yourself From Social Engineering
Now that we have seen the different types of approaches used by social engineers, let's look at how we can protect ourselves and our organization from social engineering attacks.
Install email & spam filters
Though spam filters cannot catch highly targeted attacks, they will prevent most of the spam and malicious emails from reaching your account.
Keep Antivirus and firewall updated
Similar to spam filters, an updated antivirus software will protect against most of the common viruses, trojans, and malware.
Ask for verification
Always ask for verification when someone calls you claiming to represent an organization, for example your bank. Never share confidential details such as credit card numbers or passwords over phone or email.
Create awareness
The best way to prevent your organization from getting exploited is to create security awareness programs. Educating your employees is a great long-term investment to keep your company secure.
If it seems too good to be true, it is
Finally, if something sounds too good to be true, it usually is. Never trust strangers promising to get you rich quick. As someone once said, “trying to get rich quick is the quickest way to lose all your money”.
Conclusion
Social Engineers are masters of manipulation. Unless a company’s employees are trained in social engineering awareness, it is very hard for them to avoid falling into a social engineer’s trap.
Social engineers work with people’s emotions, usually fear and greed. So whenever you are performing an action based on these two emotions, you might want to take a step back and see if you are being manipulated.
There is a famous TED talk where someone started a conversation with a spammer. Watch the full video here.
You can get a summary of my articles and videos sent to your email every Monday morning. You can also learn more about me here.
Spotify Engineering Culture - Part 1
This video is a snapshot of Spotify's approach to software enginering and people management in 2014. It has since come to be known as the 'Spotify Model'.
I put it on Vimeo originally, but that account has some issues so I put a copy here.
DISCLAIMER: This video is a historical account from 2014. It is not maintained or updated, so it is not a description of how Spotify works today.
Many people ask which tools were used. I hand-drew everything in ArtRage using a Wacom drawing tablet, and recorded the drawing and speaking using ScreenFlow.
Full drawing:
https://spotifylabscom.files.wordpress.com/2014/03/spotify-engineering-culture-part1.jpeg
Here is Part 2:
https://www.youtube.com/watch?v=vOt4BbWLWQw&feature=youtu.be
Original blog post:
https://labs.spotify.com/2014/03/27/spotify-engineering-culture-part-1/
Spotify Engineering Culture

Want to translate this? You can contribute subtitles in your language here:
http://www.youtube.com/timedtext_video?v=Yvfz4HGtoPc&ref=share
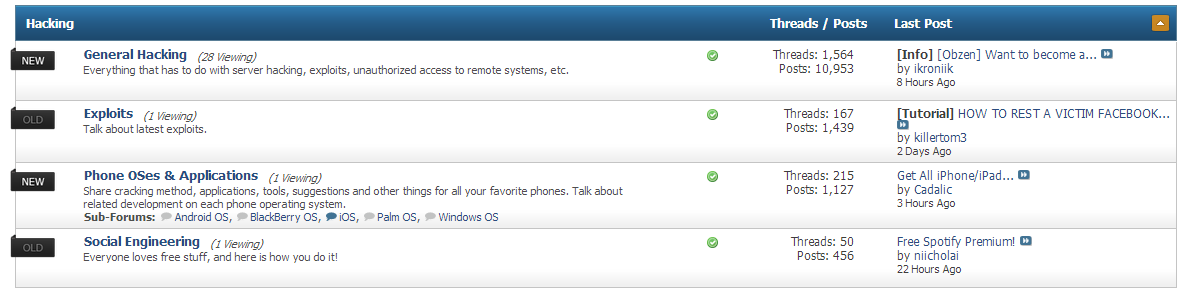
Social Engineering Toolkit
Social Engineering Definition
Free Spotify Social Engineering Internships
Spotify Social Media
| Piotr Pachołek edited Polish subtitles for Spotify Engineering Culture - Part 1 |
| Piotr Pachołek edited Polish subtitles for Spotify Engineering Culture - Part 1 |
| Piotr Pachołek added a video: Spotify Engineering Culture - Part 1 |



